Designing Security Into the SOHO Network: Architecture Over Afterthought
Network segmentation, inter-VLAN routing, and the disciplined thinking behind a secure-by-design small office environment — from threat model to operational posture.
title: "Designing Security Into the SOHO Network: Architecture Over Afterthought" description: "Network segmentation, inter-VLAN routing, and the disciplined thinking behind a secure-by-design small office environment — from threat model to operational posture." date: "2026-04-15" category: "Architecture" tags: ["Network Security", "VLAN", "SOHO", "Firewall", "Zero Trust", "Architecture"] author: "Stephen Nnamani" readingTime: "7 min" image: "/images/blog/soho-network-architecture.png"
Designing Security Into the SOHO Network: Architecture Over Afterthought
Most small office and home office networks are built for convenience, not resilience. A single flat network, one Wi-Fi password shared across every device in the building, no log visibility, and a router still running factory credentials. It works — until it doesn't. And when it stops working, the cost is rarely just downtime.
What I find professionally interesting about the SOHO environment is not its simplicity. It's the constraint. You have limited hardware, no dedicated NOC, no enterprise budget, and yet the threats are identical to those facing a mid-sized enterprise. Phishing still lands. IoT devices still get exploited. Ransomware doesn't check your headcount before encrypting your files. The constraint forces elegant, deliberate decisions — and that is where the real engineering lives.
The Architecture Decision That Changes Everything
The single most impactful architectural choice in a SOHO environment is network segmentation. Not because it is the most technically complex — it isn't — but because it fundamentally changes the blast radius of any compromise. A device on an isolated VLAN that gets infected cannot reach your file server. A smart TV on a guest network cannot be used as a pivot point into your workstation. The principle is containment: assume breach, limit movement.
In practice, segmentation at the SOHO level is achieved through VLANs on a managed switch. The moment you separate broadcast domains — workstations on one VLAN, IoT on another, guest wireless on a third — you have introduced a meaningful architectural control that mirrors what I'd deploy in a corporate environment, at a fraction of the cost.
The routing question then becomes: how do these segments communicate where they legitimately should, and how do you enforce where they shouldn't?
Router on a Stick: Elegant Simplicity Under Constraint
One architecture I favour for SOHO environments where budget precludes a Layer 3 switch is the Router on a Stick pattern. The concept is straightforward but the implications are significant.
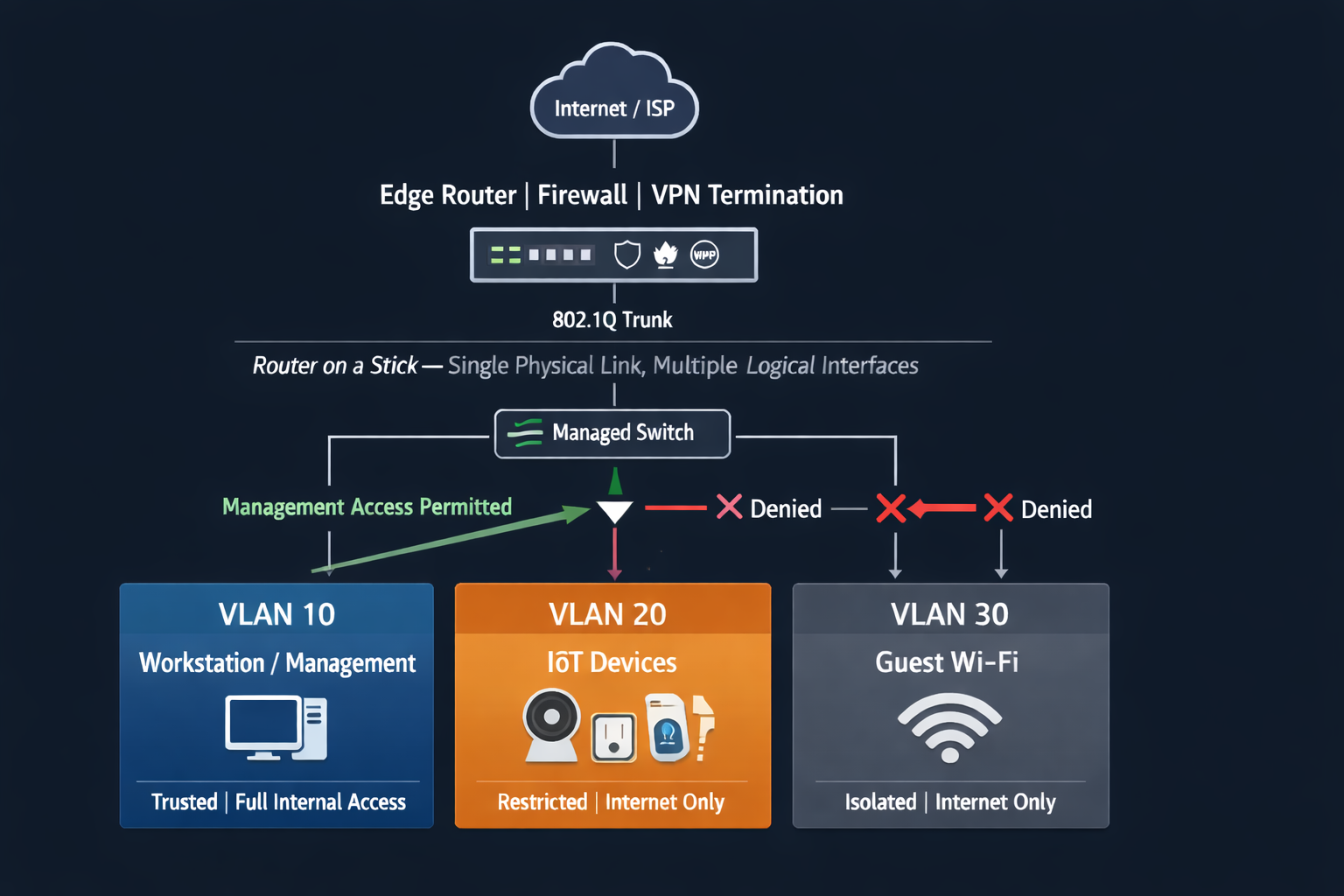
The managed switch handles VLAN segmentation at Layer 2 — creating the isolated broadcast domains. A single physical uplink connects the switch to the router, configured as a trunk port carrying 802.1Q-tagged frames for every VLAN. On the router side, sub-interfaces are configured — one logical interface per VLAN, each with its own IP address acting as the default gateway for that segment.
The result is clean inter-VLAN routing controlled entirely through the router's ACL and firewall policy. A workstation on VLAN 10 that needs to reach a printer on VLAN 30 has its traffic tagged, carried up the trunk, routed by policy, and returned — all on a single physical cable. Traffic that should never cross segment boundaries is enforced at the router, not left to chance.
Where performance demands are higher and the hardware supports it, a Layer 3 switch resolves inter-VLAN routing at hardware speed without the trunk round-trip. But for a well-designed SOHO environment, Router on a Stick delivers professional-grade segmentation on a realistic budget. The architecture scales gracefully: add a VLAN, add a sub-interface, update the ACL. The physical infrastructure doesn't change.
What I appreciate about this pattern from a professional standpoint is what it demonstrates: understanding the separation between Layer 2 and Layer 3 responsibilities, and knowing when to keep them physically separated versus when to collapse them. That judgement — not the configuration commands — is what distinguishes a security-informed network design from a default install.
Threat Modelling Drives the Design, Not the Other Way Around
Before a single VLAN is created, the right question is: what are you actually protecting, and from what?
In a SOHO context, the asset inventory is usually compact — a workstation or two, a NAS with client data, perhaps a small server, a fleet of IoT devices, and a guest network. The threat vectors are predictable: phishing, credential stuffing, rogue wireless, compromised IoT endpoints, and the occasional opportunistic ransomware delivery via email or drive-by download.
Mapping assets to threats to controls gives you a defensible architecture. It also gives you something valuable when engaging with clients or employers: a documented, auditable rationale for every decision. Not "I set up VLANs because that's what you do," but "IoT devices are isolated on VLAN 20 with an explicit deny rule preventing any outbound connection from the IoT segment to internal workstation and server VLANs — while the workstation and management VLAN retains inbound access for visibility, firmware updates, and device management. The trust is asymmetric and intentional." The threat model identifies unpatched firmware on consumer IoT as the highest-likelihood lateral movement vector in this environment.
That framing — threat model first, controls second — is how enterprise security thinking applies directly to the small office environment.
The Edge and the Endpoint: Where Discipline Shows
Network segmentation is the foundation, but the security posture is built on what surrounds it.
At the edge, the router or firewall is the policy enforcement point. Default-deny inbound, explicit allow for required services, stateful inspection, and VPN for remote access with MFA enforced. Firmware maintained. Remote management on the WAN interface disabled. These are not advanced configurations — they are baseline hygiene — but they are consistently absent in most of the environments I encounter and assess.
At the wireless layer, the choice of authentication protocol matters more than most people appreciate. WPA2-Personal with a strong passphrase is a reasonable baseline. WPA3 where the hardware supports it closes known KRACK-era vulnerabilities and introduces Simultaneous Authentication of Equals, which eliminates offline dictionary attacks against the handshake. For environments with more than a handful of users, WPA2-Enterprise with RADIUS-backed authentication separates individual credentials, enables per-user revocation, and produces an authentication audit trail — a capability that becomes important the moment you need to demonstrate due diligence to a client or an insurer.
Client isolation on the guest SSID is non-negotiable. It costs nothing to enable. It prevents a device on the guest network from communicating with any other device on that same segment — a simple but effective lateral movement barrier.
Visibility Is Not Optional
A network without log visibility is a network operating blind. In a SOHO context, "SIEM" doesn't have to mean a six-figure enterprise platform — it can mean a lightweight open-source log aggregator receiving syslog from the router, switch, and access points, with basic alerting on authentication failures, unusual outbound traffic, and rogue AP detections.
The purpose isn't compliance theatre. It's mean-time-to-detection. An organisation that discovers a compromise through a routine log review will always be in a better position than one that discovers it through a ransom note or a client phone call. The technical investment is modest. The operational return is substantial.
What This Looks Like in Practice
The architecture I described — segmented VLANs, inter-VLAN routing enforced by policy, hardened edge, authenticated wireless, centralised logging — is not theoretical. It's what I build and document as part of my homelab and consulting practice. The hardware is modest. The principles are not.
What separates a professionally designed SOHO network from a default consumer setup is not the price of the equipment. It's the intentionality behind every decision: why this VLAN, why this ACL, why this authentication protocol, why this logging destination. That intentionality is the discipline. And discipline, in security, is what holds when everything else is under pressure.
Stephen Nnamani is a cybersecurity analyst and network security practitioner with hands-on experience in SOHO and enterprise security architecture, GRC, and penetration testing. Connect on LinkedIn or explore his homelab documentation and project work at cloudtechengine.com.